Modern technology enhances vehicles, but it also brings along similar cybersecurity challenges as the smartphones, computers, and other gadgets that accompany us daily. A recent examination from the IMDEA Networks Institute in Madrid exemplifies this concern with new research on TPMS—tire pressure monitoring sensors.
Investigators discovered that tire-pressure sensors—integral to the tire-pressure monitoring systems mandated on new automobiles in the United States since the 2008 model year—transmit a unique identifier that can be consistently traced. They utilized this as a foundation for monitoring vehicle locations without the necessity of reading their license plates, as outlined in a release from the institute.
Upon uncovering this exploitable vulnerability, researchers assembled a network of radio receivers priced at $100 each. Over a span of 10 weeks, they gathered nearly six million signals from around 20,000 vehicles. They found that signals could be detected from over 160 feet away, even when receivers were situated inside structures.
“Our findings indicate that these tire sensor signals can be utilized to track vehicles and discern their movement patterns,” said Domenico Giustiniano, research professor at IMDEA Networks Institute, in a statement. “This implies that a network of low-cost wireless receivers could discreetly observe the behaviors of cars in genuine environments. Such data could disclose daily routines, including work arrival times or commuting behaviors.”
Researchers also figured out how to correlate signals to individual tires on a vehicle to enhance precision and intercept the tire-pressure readings themselves. This could disclose the kind of vehicle or indicate whether it is carrying a significant load, as stated in the release. While this poses unfortunate real-world consequences, it also resembles an intriguing plot point for a heist film. Every cloud and all that.
The susceptibility of tire-pressure sensors arises from the fact that current regulations do not mandate cybersecurity safeguards such as encryption or authentication, researchers note, emphasizing that tire-pressure monitoring systems were “engineered for safety, not security.” Regulators may not have anticipated this hazard previously, but researchers contend it is time to address it now. Or perhaps we should finally consider airless tires.
Have a tip? Reach out to us at [email protected]
**Digital Security Weakness Detected in All Vehicles Made Post-2008**
In today’s automotive realm, cars have changed dramatically, incorporating sophisticated technologies that improve safety, performance, and user experience. Nonetheless, this technological leap has also brought to light a significant issue: digital security weaknesses. Every vehicle manufactured after 2008 faces various cyber threats due to their dependence on interconnected systems and software.
**Comprehending the Vulnerability**
The digital security weakness discussed primarily arises from the growing complexity of vehicle electronics alongside the adoption of Internet of Things (IoT) technologies. Contemporary vehicles come equipped with numerous electronic control units (ECUs) that oversee everything from engine performance to infotainment systems. These ECUs frequently interact with one another and external networks, creating possible entryways for cyber intrusions.
A major vulnerability lies in the absence of strong security measures within the software governing these systems. Many manufacturers emphasize functionality and affordability over security, resulting in software that may be outdated or inadequately shielded from unauthorized access. Moreover, the use of standardized communication protocols among ECUs can leave vehicles exposed to risks if those protocols lack sufficient security measures.
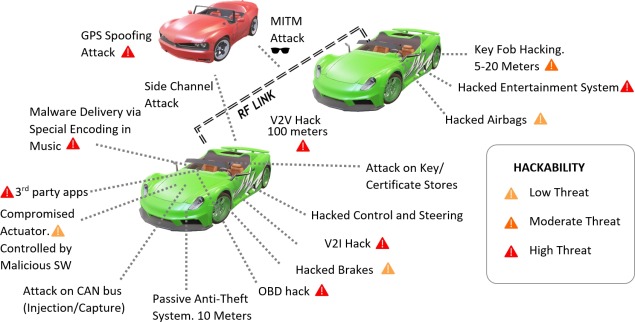
**Varieties of Cyber Threats**
1. **Remote Hacking**: With the rise of connected cars, cybercriminals can potentially infiltrate vehicle systems from a distance. This can occur via weaknesses in the vehicle’s wireless communication systems such as Bluetooth, Wi-Fi, or cellular networks.
2. **Physical Access Attacks**: Assailants may exploit vulnerabilities by obtaining physical access to a vehicle. This could involve employing specialized tools to connect with the car’s diagnostic ports or alternative access points.
3. **Malware Infiltration**: Similar to computers, cars can become infected with malware. This may happen through compromised software updates or harmful applications installed on connected devices.
4. **Data Breaches**: Vehicles collect and retain vast streams of data, including location details, driving habits, and personal information. Cybercriminals may target this information for identity theft or other malicious aims.
**Consequences of Vulnerabilities**
The ramifications of these vulnerabilities can be grave. Cyberattacks on vehicles may result in unauthorized control, leading to accidents or theft. Furthermore, breaches of personal data can cause privacy infringements and financial losses for users. The automotive sector also faces substantial reputational risks as consumers become more aware of the dangers associated with connected vehicles.
**Mitigation Approaches**
To counter these vulnerabilities, various strategies can be adopted:
1. **Routine Software Updates**: Manufacturers must give priority to frequent updates for vehicle software to rectify known vulnerabilities and bolster security features.
2. **Enhanced Security Protocols**: Implementing robust encryption and authentication methods can safeguard communication between ECUs and external networks.
3. **Vulnerability Assessment**: Regular security audits and penetration tests can pinpoint flaws in vehicle systems prior to exploitation by malicious entities.
4. **Consumer Awareness**: Raising consumer awareness regarding the significance of cybersecurity in vehicles can motivate them to take proactive steps, such as ensuring their vehicles are updated and reporting any suspicious behavior.
5. **Partnership with Cybersecurity Specialists**: Automakers should team up with cybersecurity firms to formulate and apply best practices for securing vehicle systems.
**Conclusion**
As the automotive industry continues to adopt digital technologies, the urgency of addressing digital security vulnerabilities cannot be overemphasized. All cars made after 2008 are at risk, and it is vital for manufacturers, consumers, and regulatory agencies to collaborate in enhancing vehicle security. By prioritizing cybersecurity, the industry can safeguard not only vehicle integrity but also protect consumer safety and privacy.